
To Fight Ransomware, We Need to Fill The Cultural Gap
About Continuity™
StorageGuard - by Continuity™ - is the ONLY Security Posture Management solution for Storage & Backups, helping to ensure these systems are securely configured, and compliant with industry & security standards.
How Ransomware Groups Manage To Kill Our Backups, And Why It’s Not Going Away Until We Solve The Cultural Gap
Ransomware and data theft is a cat & mouse game.
In the past two years, cybercriminals have become increasingly skillful at destroying the organizational backup first, only then locking the data – leaving victims no choice but to pay the ransom. Given how long this trend has been around, and the devastating impact of a successful attack, one would expect organizations would get things under control by now. If anything, the situation is worsening.
How could it be?
The answer is twofold: misconceptions, and culture. This post primarily focuses on the latter.
Misconceptions In-A-Nutshell
We have addressed common misconceptions in previous posts. As a recap, some of the key misconceptions include:
- Naive faith in technology – both in traditional tools, such as Vulnerability Management, Backup, and Encryption – as well as in cutting-edge offering, such as Immutable Storage and Air-Gapping. All of these technologies are, of course, important building blocks. However, without proper understanding of their strengths, limitations, and usage best-practices, and without a specific storage and backup security architecture – they could be easily bypassed by the sophisticated adversary.
- The belief that storage and backup systems are embedded too deep in the data center for hackers to reach, and that they are too obscure for them to take control of.
- Underestimating the magnitude of the attack surface.
The Cultural Gap
A cultural gap often exists between Infosec teams, and data storage & backup operations. In the worst examples, IT departments take no responsibility for the security of storage and backup.
When no explicit guidance is provided by the Infosec department, storage teams tend to see security as a hindrance to productivity, ease of management, and system efficiency. Meanwhile, security teams, fueled by the above-mentioned misconceptions, and, in particular lack of familiarity with the storage and backup attack surface, assume that the storage folks have implemented sufficient safeguards and best-practices across data storage and backup environments, and leave it at that!
Beyond that extreme, most organizations suffer from insufficient coordination between teams. Storage and Backup security baselines, are very rudimentary, leaving a significant attack surface for hackers to exploit.

Cybersecurity Culture
Security teams understand security frameworks and industry best-practices, and how they apply across networks, endpoints, and applications.
Storage and backup systems, however, remain largely unchartered territories. Existing risk detection and prevention tools do not cover storage and backup well, and in most cases, lack even the ability to connect and scan them[1]. It is therefore no wonder that Vulnerability Management and threat intelligence tools produce very few alerts regarding storage and backup. This gives rise to significant blindspots, that could cost an organization dearly.
In order to bridge the gap, infosec teams should become much more familiar with the attack surface, and with the basic security principles that are unique to storage and backup. They also need to recognize that setting up standards and expectations is part of their remit.
With storage concepts being so new to them – IT infrastructure teams can greatly help them learn!
IT Culture
On the other side of the equation, IT infrastructure folks live and breathe storage and backup, replication, data virtualization, storage protocols, networking, and recovery techniques.
Their goal is to create efficient solutions, which are fast to deploy, reliable and resilient, and easy to scale and maintain. In many respects, adding security into the blend is simply counterproductive. They claim: “too much security!” impacts performance, could lock them out, as well as increase the complexity of system settings and interdependencies.
Concepts such are “Defense in depth” – which are foundational for Infosec teams, appear in their eyes as something that could add additional dependencies and potential points of failure that could disrupt production.
Storage teams need to understand that lack of sufficient security can (and does) result in much greater opportunity for downtime and data loss! If not properly isolated, and if not enough layers of security defenses are implemented, cybercriminals can exfiltrate data directly off storage and backup environments, initiate storage denial-of-service attacks, and sabotage recovery mechanisms.
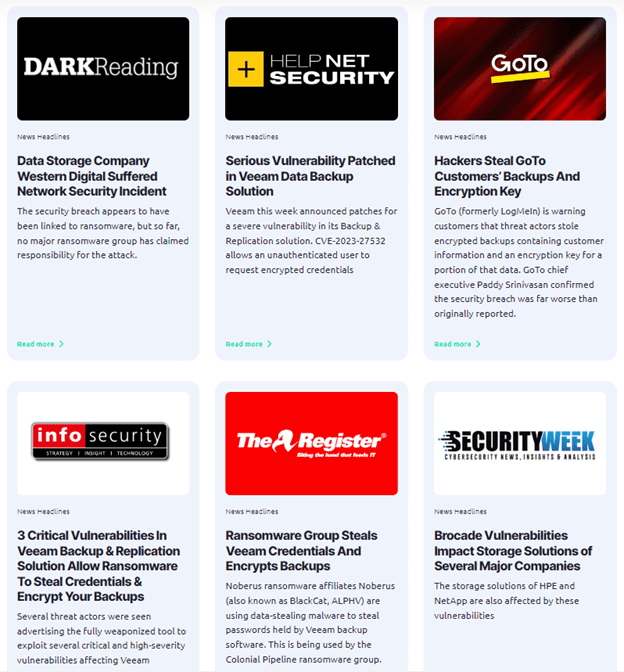
And if you don’t believe me, just check out these recent news headlines: https://www.continuitysoftware.com/resources/?resources_category=headlines
With security concepts being so new to them – Infosec teams can greatly help them learn!
The Consequences of Cultural Disparity
The result of these cultural differences? Too often, vital security duties are either not considered or are thought to have been taken care of by someone else. This responsibility gap can have serious consequences. A recent 2023 study published by Continuity, demonstrates that the average storage and backup system contains 14 security misconfigurations and vulnerabilities, 3 of which are of critical risk rating and could present significant compromise if exploited[2].
Those very same security risks are directly related to the success of the vast majority of recent cyber-attacks. These include undetected, and unpatched vulnerabilities, improper separation of backup control planes, improper hardening of storage and backup devices, insufficient supply-chain security, and many others.
What To Do About It
The good news is that with proper awareness of the gap, it is possible to witness significant and rapid improvement in storage and backup security. Here are some of the steps you can take to quickly regain control:
- Discover the maturity-level of your organization using a storage and backup risk assessment. You can definitely use external consultants; make sure to ask them to use methodologies and tools specifically designed to evaluate storage and backup systems. The risk assessment should help you answer questions such as:
- Do our security incident-response plans cover storage-centered attacks?
- Is there secure event logging and auditing of storage infrastructure?
- Do you have an established security baseline process for storage infrastructure?
- How well do we manage storage and backup inventory, and do we keep track of their security posture?
- All of these questions and additional ones, are covered in this checklist.
- Close any discovered knowledge gaps your Infosec and IT operations teams have. There are excellent resources you can use, including the NIST 800-209 Special Publication: ‘Security Guidelines for Storage Infrastructure’, and the upcoming ISO 27040 – focused solely on securing storage & backup systems.
- Define clear ownership, roles, and responsibilities that best match the way your organization is operating. For example: The cybersecurity team defines the baselines, regularly reviews the baselines, and works to improve controls; IT operations implements the required actions and provides automated evidence reporting; and both teams take part in joint incident response testing such as annual tabletop cybersecurity exercises, and annual recovery testing.
- Employ automation for storage and backup risk-posture management. Many of the required capabilities can be obtained by using storage-specific commercial tools[3]
How secure is your storage & backup environment?
Find out in this 2-minute Ransomware Resiliency Assessment for Storage & Backups, and receive a maturity score and practical recommendations.
https://www.continuitysoftware.com/ransomware-resiliency-assessment/
[1] Storge and backup often relies on proprietary hardware and storage OS, which are not detectable or scannable by existing tools. Many of the protocols used, are completely unsupported (e.g., NDMP, FCIP) and quite a few are not even IP-based. In addition, storage and backup software resides in unusual and unexpected places, such as hypervisor plugins, dedicated network adapters, storage appliances, etc.
[2] The survey comprised of 245 customer environments, spanning around 8,500 storage and backup devices, and analyzing almost 10,000 different misconfigurations. Around 60% of the environments were in the financial-sector, and the rest were in healthcare, telecommunication, retail, media and other sectors.
[3] Such as Continuity StorageGuard has been designed to comprehensively scan all data storage, storage management, and backup systems to look for vulnerabilities and security misconfigurations. It offers enterprises complete visibility into storage and backup blind spots, automatically prioritizing the most urgent risks.
Talk To An Expert
It’s time to automate the secure configuration of your storage & backup systems.