
Storage security mythbusting: 4 myths CISOs still believe, and why they’re wrong
About Continuity™
StorageGuard - by Continuity™ - is the ONLY Security Posture Management solution for Storage & Backups, helping to ensure these systems are securely configured, and compliant with industry & security standards.
Experience is the mother of wisdom, or so the famous proverb goes. And there’s definitely something to that: the more of life we’ve experienced, the more knowledge we’ve gained.
But as with most things in life, there are always shades of grey, and they make all the difference.
While experience does teach us a lot about life, we all have preconceived notions, misconceptions, and misinterpretations that shape the way we absorb life’s lessons. Life also has a way of distracting us with the daily grind so that we tend to forget that our reality is a fast-changing one that often upends beliefs we hold to be true.
This is especially true when it comes to storage, and more specifically, storage security. Many of the industry’s most experienced CISOs and security experts can spend their entire careers believing in myths and misconceptions that have no bearing on reality.
This article is dedicated to debunking a few of the more common – and dangerous – myths that populate the cybersecurity industry.
If you or your team believe in any of the myths that we’re about to list, you’re in good company, but you just may be exposing your organization to unknown risks.
Feel free to check out the list below, or skip straight to our cheat sheet for a more condensed version of tips on busting these myths, so that your organization remains safe and sound.
Myth #1: Storage is too deep to reach and too obscure to attack

The first common misconception held by many CISOs is that their storage systems are hidden away and hard to detect, and it would be extremely difficult for attackers to get anywhere near them. So why bother securing them?
This is, of course, very far from the truth. It’s much easier than you think – learn just how from these real-life nightmares.
It is much easier to get storage education these days than it used to. Anyone can register for online courses. It’s also easy to get access to storage labs; what used to cost millions in the past can now be built by downloading storage simulators of even the most high-end storage equipment that can be leveraged to search for vulnerabilities and plan breaches for your storage layer.
There are many ways to penetrate the storage layer from the outside. A dead-simple, yet highly effective one is looking up your storage admins on LinkedIn and finding their work email. Social engineering tactics can fool even the most seasoned storage admin (e.g., forging an email from their trusted vendor rep, encouraging them to try out a new tool), and all it takes is a click on a fictitious link in an email, to dump malware into the network.
Once the storage admin falls prey, attackers can access the admin’s browser history, and obtain the login credentials to the storage management console. Perhaps you didn’t harden the access to the storage console; maybe even the default passwords are still available; session cookies have not been cleared; session timeouts have not been deployed. From here the road to directly controlling the storage device is smooth sailing for the predator.
How about getting into your storage systems through the vendor support network? Many of the clients we work with will claim they have disabled all those options but in reality, they are often enabled. An attacker can potentially impersonate an update server, or hijack a support network connection to have their own custom code run on your storage and backup systems.
Reality check #1: It’s much easier to get into the storage and backup layers than you think! Modern attackers can hack storage systems with ease
Myth #2: I have backup. What can possibly go wrong?
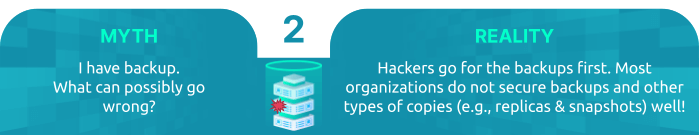
Storage backup copies can definitely save the day when something goes wrong. But many security execs don’t realize just how complex backup environments can be. Most think it’s only about tape (or even disk) backup tools – but these systems are notoriously slow, so in reality data recovery often relies on multiple, different tiers, each offering different recovery speeds and representing additional layers of protection.
The first tier is storage-based snapshots, which can be restored very quickly. However, what many CISOs don’t know is that once hackers gain access to the storage system, they can easily wipe out those snapshots.
The second tier is replication to remote sites that can be restored relatively quickly. But often the same admin credentials used to gain access to production servers can also be used to access the replicas, which as you probably guess, means that hackers with admin credentials will often delete the replicas, just as soon as they finish with the production storage.
The last line of defense is the actual backup systems themselves, which could be super slow to restore. Here again, poor separation of duties often means that admin credentials for the data system will be the same for the backup systems and hackers will usually immediately delete them upon penetration.
Even immutable storage can be ‘poisoned’, enabling hackers to change the configuration of backup clients and gradually replace stored data with meaningless information.
You can learn more about poisoning and how you can prevent it in this video.
Reality check #2: Hackers go for the backups first. Most organizations do not secure backups and other types of copies (e.g., replicas and snapshots) well!
Myth #3: We already use vulnerability scanning tools that cover storage
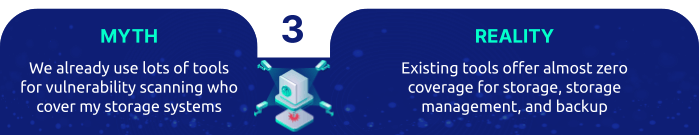
Most organizations already invest in vulnerability management. But, what most infosec folks don’t know is that these tools don’t provide coverage of storage and backup systems.
Storage arrays, Storage network elements, Data Archiving Appliances, and other storage and backup elements, all have Common Vulnerabilities and Exposures (CVEs) regularly identified, published, and patch. Yet commercial Vulnerability Management solutions in the market provide little or no coverage to these layers.
In addition, since storage and backup use less-known protocols (some are completely non-IP), malicious actors can access the storage and backup layer completely unnoticed.
For example, they can copy or clone critical services that boot from the storage network. The copies can be used to boot cloned systems in separate environments (even outside your organization) – such as your development or testing, so that they can use VMs to inspect the content outside of the OS.
In this manner, they completely circumvent traditional vulnerability management tools. They can even leverage backup software to create copies of the cloned devices to cloud environments and download them from there to avoid inspection by Data Loss Prevention (DLP) tools!
If intrusion detection and advanced threat intelligence tools don’t track how storage devices connect to servers, or monitor configuration changes such as deleted snapshots and backup policy changes, hackers can easily modify and steal data without leaving a trace.
Reality check #3: Existing tools offer almost zero coverage for storage, storage management, and backup.
Myth #4: Data secured by multiple layers cannot be breached
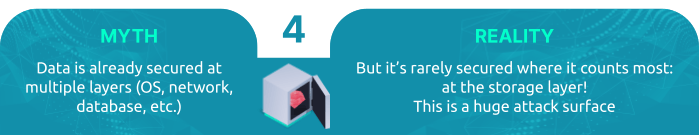
The practice of data encryption helps ensure that no one can read your data if a storage disk is lost, misplaced or stolen.
The practice of storage security helps ensure attackers cannot compromise central storage systems by exploiting vulnerabilities, misconfigurations or weak security settings, or by deploying malware.
In this article you can find out more about these two practices and get some real-life storage attacks examples.
Reality check #4: Data is rarely secured where it counts most: at the storage layer! This is a huge attack surface.
Summary
Sure – securing storage won’t prevent attacks – but nothing else would either! You must prepare for a scenario where attacks will succeed. Storage and backup are your last line of defense, and they must be properly secured. If they are – you can be confident that you’ll be able to recover. If not – you run the risk of losing your business. However, this infrastructure layer hasn’t been given its rightful place at the cybersecurity table.
Many myths and misconceptions regarding protection, backup and recovery have caused even the most knowledgeable of infosec execs to put that at a low priority.
The unfortunate truth is that many of these beliefs are either no longer relevant, or never were.
Being uninformed creates a huge blind-spot that could allow adversaries to clone your data, destroy your environment and its recovery layer.
Experts believe that data-targeted attacks won’t be limited to ransomware alone – and that the future holds the potential for data-integrity attacks, where adversaries (either hackers, cyber terrorists, or nation states) might modify your data for far greater gain than ransom.
Forward-looking security and data folks would do well by educating themselves on the current realities on the ground when it comes to data storage security.
There are a number of critical steps that can be taken to reduce the risk of storage system breaches. It all starts with a clear understanding of your environment’s attack surface and how it functions.
Great resources exist … For example, this NIST report
NIST Special Publication on Securing Storage
The guide – co-authored by Continuity’s CTO – provides an overview of the evolution of storage technology, recent security threats, and the risks they pose.

Talk To An Expert
It’s time to automate the secure configuration of your storage & backup systems.