
5 Takeaways From The New Gartner Hype Cycle For Storage & Data Protection 2022
About Continuity™
StorageGuard - by Continuity™ - is the ONLY Security Posture Management solution for Storage & Backups, helping to ensure these systems are securely configured, and compliant with industry & security standards.
Background to the Gartner Hype Cycle For Storage & Data Protection
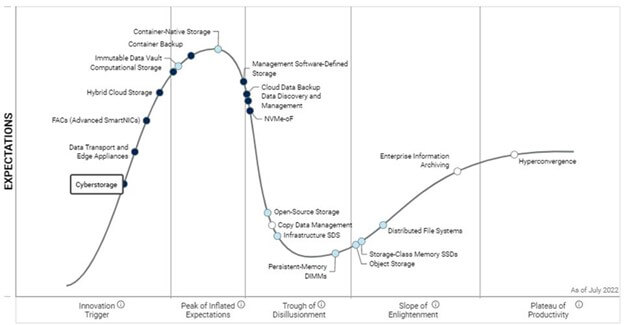
The latest 2022 Gartner Hype Cycle report for Storage and Data Protection has just been published and I’m thrilled to see that Cyberstorage is steadily progressing up the firm’s innovation curve.
In addition, Continuity is listed as a featured vendor (apologies for patting ourselves on the back!!!)
For those who don’t know, Gartner’s Hype Cycle represents the maturity and adoption of emerging technologies, and how they are potentially relevant to solving real business problems.
In this particular report, Cyberstorage is defined by Gartner as “protecting unstructured storage system data against ransomware attacks through early detection and blocking of attacks”.
Gartner explains why this has become such a hot topic.
Cyberstorage; The New Kid On The Block
“Ransomware attacks are becoming increasingly common, requiring the adoption or deployment of cybersecurity tools for active defense.
Although numerous solutions are available for endpoint protection, back-end protection largely fails due to a lack of solutions. Network-attached storage (NAS) and scale-out file system storage provides inadequate protection from malicious deletion or encryption of data.
Cyberstorage provides active defense against cyber attack on unstructured data.”
Cybersecurity threats dominated IT concerns in 2021 and are growing in occurrence and magnitude. The effect of ransomware is enormous and destructive, impacting areas such as loss of business and recovery costs. Ransomware climbed an unprecedented 105% in 2021 over 2020 to 623.3 million attacks worldwide.
According to Gartner, “ransomware attacks will become so common that I&O leaders will have to assume data cybersecurity responsibility and adopt new approaches for active defense. While storage infrastructure can be one of the most impacted solutions attacked by ransomware, it initially receives limited attention by security and storage leaders”.
What Does NIST Have To Say About Storage & Backup Security
To address this potential gap, NIST released Special Publication (SP) 800-209, Security Guidelines for Storage Infrastructure, which includes comprehensive security recommendations for storage & backup infrastructures.
Storage technology, just like its computing and networking counterparts, has evolved from traditional storage service types, such as block, file, and object.
This evolution has taken two directions:
- The first is along the path of increasing storage media capacity (e.g., tape, Hard Disk Drives, solid-state drives (SSD)
- And the second is along the architectural front, starting from direct-attached storage (DAS) to the placement of storage resources in networks accessed through various interfaces and protocols to cloud-based storage resource access
Accompanying the architectural evolution is the increase in management complexity, which subsequently increases the probability of configuration errors and associated security threats.
How Widespread are Storage Vulnerabilities And Backup Misconfigurations?
Last year, we published a research report that provided an analysis of the storage and backup vulnerabilities, and storage & backup security misconfigurations.
We analyzed multiple storage & backup systems and vendors, including Dell EMC, IBM, Hitachi Data Systems, Cisco, Brocade, NetApp, and others.
The report identified 6,300 security risks, with a single storage or backup device containing 15 vulnerabilities – many of them high risk.
As a result of the increased focus on storage vulnerabilities and backup misconfigurations, there has been an emergence of new cyberstorage products that are designed to identify, detect, protect, respond to and recover from ransomware attacks.
Some vendors position traditional storage technologies like snapshots, as a single answer for ransomware protection, which is completely inadequate to meet the new challenges ransomware brings.
Cyberstorage products differentiate their capabilities by aligning with NIST Special Publication (SP) 800-209, Security Guidelines for Storage Infrastructure.
5 Takeaways From Gartner Hype Cycle & NIST
- Assign higher priority to improving the security of enterprise storage and backup systems
- Build up knowledge and skill sets – and improve collaboration between your Infosec and IT infrastructure teams
- Define comprehensive security baselines for all components of storage and backup systems
- Use automation to reduce exposure to risk, and free up your time. Storage vulnerability management solutions can solve this problem, by automatically scanning, prioritizing, and remediating vulnerabilities & security misconfigurations
- Run frequent and more comprehensive testing of storage security, backup protection – and your ability to recover from an attack. This will not only improve confidence, but will also help identify key data assets that might not meet the required level of data protection
Download the NIST guide to get a set of practical recommendations on securing your storage & backup systems.
NIST Special Publication on Securing Storage
The guide – co-authored by Continuity’s CTO – provides an overview of the evolution of storage technology, recent security threats, and the risks they pose.

Talk To An Expert
It’s time to automate the secure configuration of your storage & backup systems.