
Best Practice Guide: Meeting Backup Requirements for Cyber Insurance Coverage
About Continuity™
StorageGuard - by Continuity™ - is the ONLY Security Posture Management solution for Storage & Backups, helping to ensure these systems are securely configured, and compliant with industry & security standards.
Cyber insurance provides a cushion to fall back on in a successful cyber-attack, providing coverage for damages caused by data loss.
Insurance companies carry out risk assessments which determine your premiums, coverage limits, and whether or not you qualify for cyber insurance.
In order to manage risks, insurance companies require policyholders to set up and maintain cyber-security standards to qualify for cyber insurance.
As cyberattacks continue to evolve, insurance companies are now adding measures such as immutability, regular backup testing, and multi-factor authentication for backups, as a requirement to reduce cyber liability. In addition, if you have active measures in place to protect your backups, it will help you negotiate lower insurance premiums.
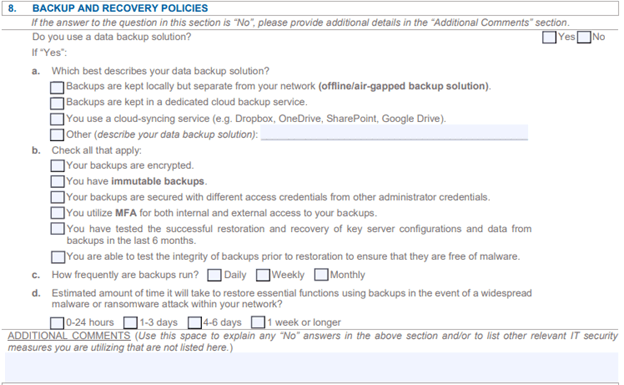
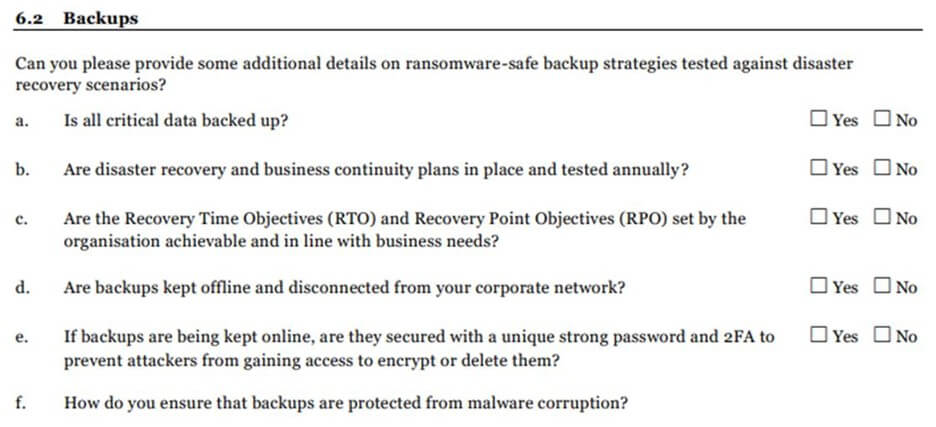
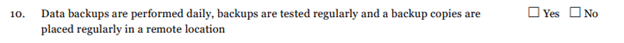
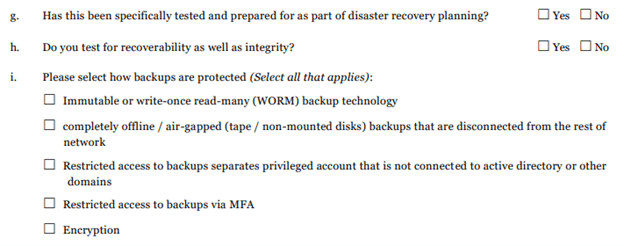
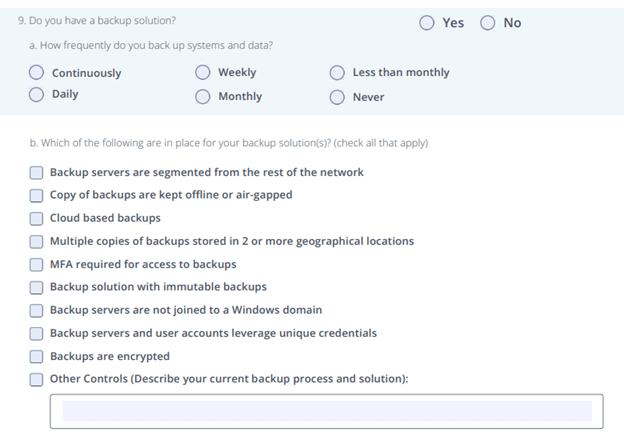
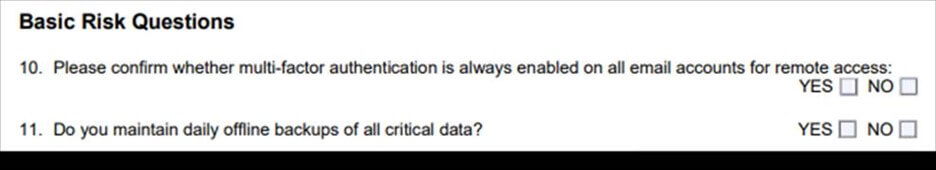
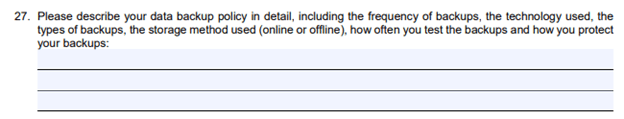
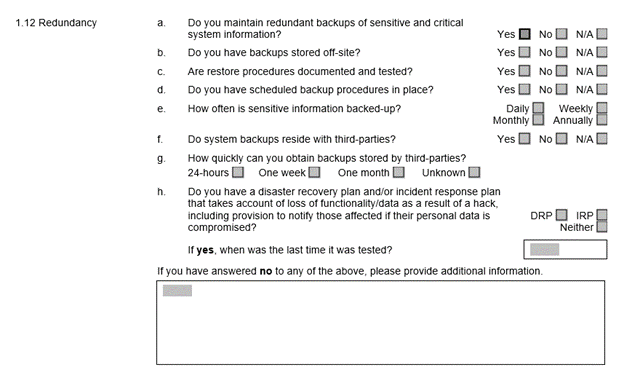
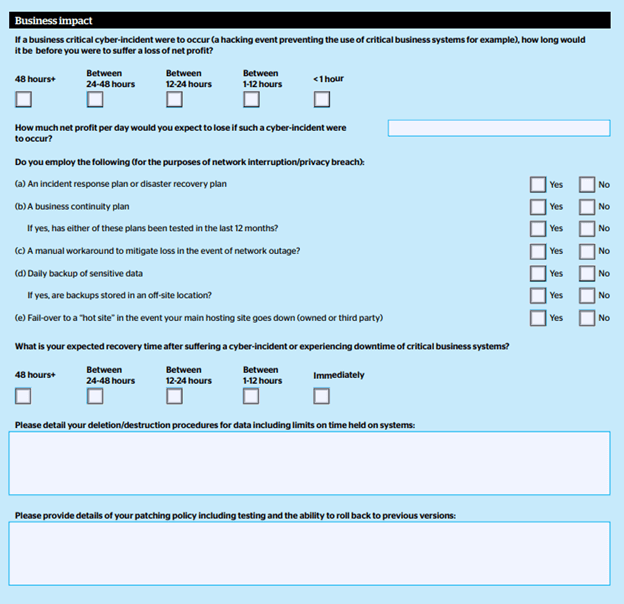
While these measures vary depending on the insurance company, here are a few examples of cyber insurance application forms, in which they include specific questions on backup and data recovery policies.
Tokio Marine HCC
Chubb

Corvus
https://info.corvusinsurance.com/hubfs/Corvus%20Smart%20Cyber%20Application.pdf
Victor Insurance
https://www.victorinsurance.ca/en/pl/resources/pl-applications/cyber-applications.html
Hiscox
QBE
An 8-Point Checklist for Backup Protection
A ransomware attack is a horrible time to discover that your backups are not secure, so to help, here’s an 8-point checklist to determine whether your backups are sufficiently secured.
- Do your security incident-response plans include cyberattacks on your backups? If so, what’s included:
- Recovery from a complete wipe of a storage array
- Recovery from a complete corruption of the SAN fabric configuration
- Recovery from ransomware
- Is there a complete inventory of your storage and backup devices, that includes the current security status for each one?
- All backups, archive environments, storage arrays (block, file, object), and SAN switches
- Storage software versions (storage OS, firmware deployed), and, in particular: patching status, known CVEs, and actual resolution status
- What is backed up? Where? How?
- Which storage & backup protocols are allowed? Are all obsolete and insecure protocols disabled
- Is there comprehensive and secure event logging and auditing of your backups?
- Including: central log services, redundant and tamper-proof records, and redundant and reliable time service
- Are you able to audit the configuration changes?
- e.g., what changed and when – in device configuration, storage mapping, and access control?
- Is there a well-documented, and enforced separation of duties for your backups?
- e.g., separate admins for storage, backup, and disaster recover in each environment
- Are all storage and backup administrative-access mechanisms documented?
- e.g., which APIs are open, how many central storage management systems can control each storage device, and are there any servers or OS instances that can control storage
- Are existing mechanisms for ransomware protection, air-gapping, and copy-locking used?
- Is there an audit process to verify they are correctly deployed at all times?
- Is the security of your backups regularly audited?
- Does this audit process include: SAN communication devices, storage arrays (block, file, object), server-based SAN, and backup?

Take the 2-minute Ransomware Resiliency Assessment for Backups, to receive your maturity score and practical recommendations.
Talk To An Expert
It’s time to automate the secure configuration of your storage & backup systems.